WannaCry cyberattack: Here is how to protect your computer, and more
WannaCry is without doubt the biggest ransomware attack the world has ever seen, and here's how to protect
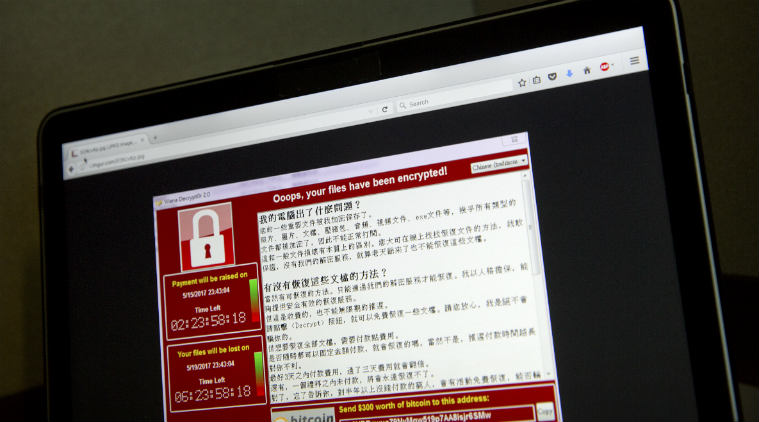 WannaCry attack: Here’s how to protect your PC, and what to do if your computer gets infected. (Source: AP)
WannaCry attack: Here’s how to protect your PC, and what to do if your computer gets infected. (Source: AP)
WannaCry is without doubt the biggest ransomware attack the world has ever seen. Though the impact has been thwarted to a certain extent, it is feared that ransomware could be back in a big way.
Sunil Gupta, president and chief operating officer of Paladion Networks, explains how to tackle this new menace. He says the bug is tapping into NSA’s ETERNALBLUE exploit, originally devised to leverage Microsoft Windows SMB vulnerability (addressed in MS17-10) with the creators of WannaCry integrating this critical exploit into its worm module or initial dropper.
The ransomware also observed in making use of NSA’s DOUBLEPULSAR backdoor.
What are the affected products?
All Windows versions before Windows 10 are vulnerable if not patched for MS17-010. Windows XP and Windows Vista users are completely vulnerable as both these operating systems no longer receives updates and security patches. As a special case, Microsoft has pushed updates for older operating systems and promised more. Refer the listed CVEs in IOCs – WANNACRY RANSOMWARE.xlsx
How does it impact you?
Once the initial worm module is introduced to a system it creates two threads — one that scans hosts on the LAN, and another that gets created 128 times and scans hosts on the wider Internet. The LAN-based scanning happens using the port 445 and attempts to exploit the discovered systems using MS17-010/ETERNALBLUE.
The second thread scans the Internet by generating random IP addresses. If connection to port 445 on that random IP address succeeds, the entire /24 range is scanned, and if port 445 is found open, exploit attempts are made. So, if the target network has the vulnerability unpatched, then there is a high chance it will get affected.
How can this be prevented?
Despite the exploits/vulnerabilities being exposed a month back, so many systems were still unpatched. To protect from this ongoing mass exploit and propagation one can do the following:
1. Install all available OS updates including to prevent getting exploited
2. Manually disable SMBv1 via modifications made to Windows Registry by following these steps:
a. Navigate to: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\LanmanServer\Parameters
b. Look for Value: SMB1
c. Modify Data: REG_DWORD: 0 = Disabled
3. Restrict inbound traffic to open SMB ports (ports 139, 445) which are publicly accessible / open to Internet.
4. Block the IPs, Domains, Hash values that are involved in spreading this malware. Please refer the attachment – IOCs – WANNACRY RANSOMWARE.xlsx for details.
5. Implement endpoint security solutions. The ‘AV Signature Name’ section under IOCs – WANNACRY RANSOMWARE.xlsx can be referred.
6. Keep an offline backup of critical data on desktops and servers.
7. Organisations should block connections to TOR nodes and TOR traffic on network (IOCs – WANNACRY RANSOMWARE.xlsx).
What action should the Bank/User/Customer take?
Install all critical patches.
Review any traffic towards ports 139, 445. Block if not required.
It is highly recommended that the provided list of threat indicators (IOCs – WANNACRY RANSOMWARE.xlsx) should be blocked at perimeter devices such as firewall, proxy etc. and Email Security Gateway immediately. However, kindly note:
You shall act upon this advisory/IOC-list at your own discretion after conducting risk analysis in your specific environment.
The advisory/IOC-list is time sensitive in nature and may be overridden in subsequent updates from our side as new information is received on the threats.
What should be done if a node has found infected?
1.Disconnect the infected system(s) from the production network.
2.Perform a full Antimalware scan on the system(s) by adhering the following:
F-SECURE-https://www.f-secure.com/en/web/home_global/online-scanner
MCAFEE-http://www.mcafee.com/uk/downloads/free-tools/stinger.aspx
MICROSOFT-http://www.microsoft.com/security/scanner/en-us/default.aspx
SOPHOS-https://www.sophos.com/en-us/products/free-tools/virus-removal-tool.aspx
TREND MICRO-http://housecall.trendmicro.com/
You can refer IOCs -WANNACRY RANSOMWARE.xlsxfor identifying additional Antimalware tools with successful detection for further scanning and disinfection.
You can refer IOCs -WANNACRY RANSOMWARE.xlsxfor identifying additional Antimalware tools with successful detection for further scanning and disinfection.
3. Block the supplied indicators (IPs, domains, and hash values)at the gateway devices.
4. Try attempting to decrypt any encrypted files using decryption tools such as Trend Micro Ransomware File Decryptor, nomoreransom.org/decryption-tools.html
5. Removal script for DoublePulsar impant (if found): github.com/countercept/doublepulsar-detection-script
6. Restore data from the most recent backup made